The complete insider threat detection and response playbook
Identify and contain internal risks before they escalate by using a NIST-aligned response framework designed to spot threats from users with legitimate access.
You’re managing sensitive data across hundreds of systems, balancing access, speed, and trust while keeping your org secure. Insider threats feel rare ... until they aren’t.
Because these threats come from users with legitimate access, they’re harder to spot, slower to contain, and more damaging when missed. Most orgs don’t have a real plan until it’s too late.
This guide gives you a step-by-step response framework for detecting and containing insider threats based on real-world incidents, forensic best practices, and NIST-aligned workflows. No fluff. No fearmongering. Just a clear playbook for staying ahead of internal risks.
More IT resources
Guide
The IT leader’s playbook for turning compliance into a competitive advantage
Audit fire drills are an infrastructure problem, not a compliance one. Get the playbook IT leaders use to automate evidence collection and pass audits faster.
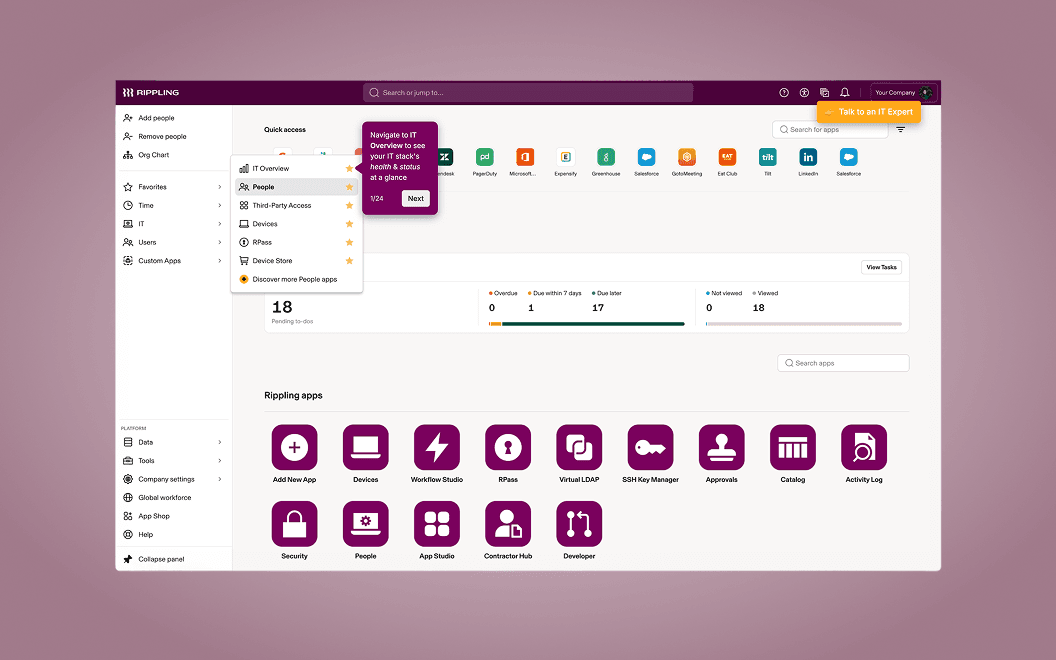
Tool
Explore Rippling IT with an Interactive Demo
Identity, devices, and security in one platform. Take a tour at your own pace below.

Guide
The 10-point access hygiene checklist
Catch and fix hidden access risks before they turn into costly breaches. This checklist helps you spot gaps early, tighten controls, and reduce unnecessary spend.
Guide
The 2025 IT Ops Report: Quantifying the impact of software proliferation
Reclaim your IT team’s time and reduce the "execution tax" by identifying the hidden costs of software sprawl and benchmarking your operational maturity.